It is unlikely that you could find a Windows user who is not aware of what a ransomware infection is, and that is because this kind of malware has been dominating for the last couple of years. Some threats are more aggressive and well-known than others (e.g., Wannacry, Badrabbit, or NotPetya), but even those that spread on a much smaller scale cannot be underestimated. Our research team has recently discovered an infection that goes by the name Zenis Ransomware, and although it appears that the attacks of this malware were short-lived, it certainly left a mark. Just like all other file-encrypting ransomware, this infection corrupted personal files, but what is unique is that the infection also deleted system backups. While removing Zenis Ransomware is crucial, that is not a solution that would ensure full decryption of personal data.
The malicious ransomware spreads using hacked RDP servers
The distribution of Zenis Ransomware is an extremely important topic to discuss. This infection does not appear out of thin air, and it does not spread itself. According to the latest information, this threat is most likely to slither in using hacked remote desktop connection servers. In many cases, however, malicious threats are distributed using several different methods, and so it is impossible to determine how exactly this threat would approach every single target. It is important to note that file encryptors are often spread using the backdoor opened via the email inbox. In this situation, the infection’s launcher is concealed as a normal file that supports the misleading message (e.g., if the message suggests printing a postal delivery confirmation, the malicious launcher might be represented as a Word Document file or a PDF), and it is enough to open it to execute the infection. The victim is not alarmed about the execution of malware unless their operating system is protected by reliable anti-malware software that is up-to-date and can successfully identify and delete Zenis Ransomware before it initiates the encryption of personal data.
Zenis Ransomware might encrypt thousands of files
Once the malicious ransomware is executed (the original name of the threat is “iis_agent32.exe”), it starts the encryption process as soon as the encryption key is obtained. According to the information gathered by our team, the threat is capable of encrypting 204 different types of files, among which are .txt, .doc, and .ppt files. Zenis Ransomware is set to encrypt photos, media files, documents and other sensitive information, and besides encrypting files, it also renames them. Once the file is corrupted, its name is changed to a name that goes in the “Zenis-[2 random characters].[12 random characters]” format. Once that is done, the threat scans the system for backups, and these are the formats of the targeted backup files: .bak, .bak2, .bak3, .bff, .bkf, .bkp, .bkup, .bup, .edb, .ful, .obk, .old, .qic, .rbk, .sqb, .stm, .tibkp, .trn, .v2i, .w01, .wbb, and .win. This is why relying on system backups is not a good idea. It is much safer to use external drives or online storage to back up the copies of all personal files, and the activity of ransomware is not the only reason to take care of that. Backups can save you in the event of technical damages or the loss of the device. If backups existed, you would not need to think about the decryption of files at all.
The ransomware was created to extort money from Windows users
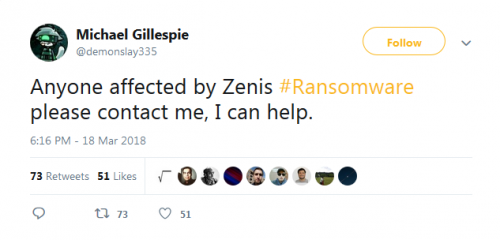
Once Zenis Ransomware completes the encryption of data, it creates “Zenis-Instructions.html,” a file that should have copies in every folder containing encrypted files. According to the message represented via this file, the victim of the infection must perform six steps to ensure that files are decrypted. The first step is sending the HTML file with one encrypted file to TheZenis@Tutanota.com or TheZems@MailFence.com (alternatives include TheZenis@Protonmail.com and TheZenis@Mail2Tor.com). In the second step, the creator of the ransomware responds with the decrypted file attached to the email. Next, you need to confirm that the decryption happened, and that is when the “price” of the ransom is revealed. The request to pay the ransom should include information regarding the payment because it is not revealed in the original ransom note. In the final step, you should use a program called “Zenis Decryptor” and a unique “Private Key” to decrypt files. The price of the ransom might be huge, or it could be small, but, in either case, paying it is not recommended because cyber criminals are not trustworthy, and they are likely to abandon you as soon as the ransom is paid. At this point, legitimate file decryptors cannot help, but the self-proclaimed “Ransomware Hunter,” Michael Gillespie, suggests there is a solution.
How to remove Zenis Ransomware and protect the operating system
If the ransomware has invaded the operating system, removing it is crucial, and even if the decryption of files is not possible, this threat most go. Hopefully, all files are backed up, and there is no need to worry about losing them. If that is not the case, you might be thinking about communicating with cyber criminals and obeying their demands. If this is the risky route you take, look for legitimate and free file decryptors first. In general, paying the ransom is not recommended because cyber criminals cannot be held accountable, and once they get the ransom, it is unlikely that they would waste their time communicating with the victim anymore. Moreover, the deleted backup files cannot be restored regardless of what you do. The guide below presents the steps that must be taken to have the threat eliminated, but it is best to install anti-malware software because it will automatically delete Zenis Ransomware, and, simultaneously, it will start protecting your operating system against the threats that might target it in the future. If you employ reliable security software, install all security updates as soon as when they come, and back up files, you should be able to stand strong against any ransomware.
Removal Instructions
N.B. The ransomware might kill Task Manager and Registry Editor. In this case, you might have to reboot the system to Safe Mode before you proceed.
- Delete all recently downloaded suspicious files.
- Delete the file named iis_agent32.exe (its location can be random).
- Tap keys Win+R to launch the RUN dialog box.
- Enter regedit.exe into the box to launch Registry Editor.
- Move to HKCU\SOFTWARE\ZenisService and HKCU\SOFTWARE\Wow6432Node\.
- Delete the key named ZenisService.
- Delete all copies of the Zenis-Instructions.html file.
- Empty Recycle Bin and then perform a full system scan to check for leftovers.