Do you know what Windows Foolproof Protector is?
The Rogue.VirusDoctor family rapidly expands its “army” and makes clones one after another. The latest clone of the family is Windows Foolproof Protector, which is a clone of Windows Component Protector and other malware, and which supposedly protects the systems from different threats. Delete Windows Foolproof Protector at once after spotting it in your computer’s screen if you have not done that yet.
This rogue will treat your system in a very harsh way. It will stop the processing of some executes which are necessary to be activate in the system in order to find the system’s infections. Windows Foolproof will also disable Registry Editor and Task Manager, and you will lose access to the Internet. It will be done in order to keep you away from finding important information about how Windows Foolproof Protector should be deleted from the system.
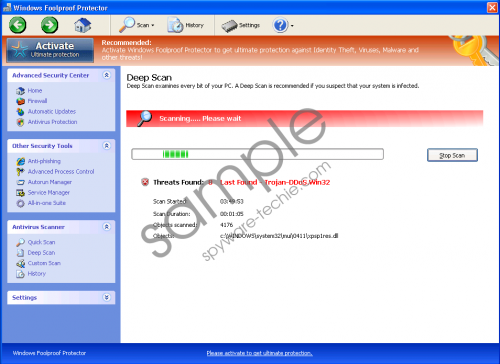
In addition, Windows Foolproof Protector is more persistent than you may think. The rogue initiates imaginary scans and provides you with simulated results saying that the system is under threat. Fake Trojans and other imaginary infections are presented as terrible threats damaging your system and sending your sensitive information to third parties. For example, you will get a list of such “threats” as Server-FTP, Trojan-DDoS.Win32, Trojan-Clicker and others. Moreover, do not get hooked on the fake notification given at the bottom of the scan table saying that:
Programs classified as Trojan download and install versions of malicious programs, including Trojans, and Adware, on victim computers.
Nonetheless, Windows Foolproof displays annoying pop-ups in the task bar , and you cannot get rid of them. Please find three examples of a bunch of imaginary threats presented by Windows Foolproof Protector, and pay attention to the last warning message saying that C:\program files\internet explorer\iexplore.exe is a threat. Iexplore.exe is the most important executable necessary to run Internet Explorer, and it is not harmful at all. Ignore such fake message, and do not trust their content:
Error
Trojan activity detected. System data security is at risk.
It is recommended to activate protection and run a full system scan.Error
Keylogger activity detected. System information security is at risk. It is recommended to activate protection and run a full system scan.Warning
Firewall has blocked a program from accessing the Internet
C:\program files\internet explorer\iexplore.exe
is suspected to have infected your PC. This type of virus intercepts entered data and transmits them to a remote server
Windows Foolproof Protector was created for one reason that is to gather financial information from Windows users and to steal their money. The malware will offer its fake “full” version which will supposedly remove all threats which are imaginary. Do not trust this malware, and do not pay for it, because you will lose your money voluntarily but will not remove the only possible threat in the system which is Windows Foolproof Protector.
It is essential to delete this malware. For easier removal of the rogue and disablement of annoying pops, use a registration key. It will also restore the processes which were disabled by the malware, and you could start removing the rogue. After entering the key, Windows Foolproof Protector does not disappear from the system but “waits” until you remove it.
Registration key: 0W000-000B0-00T00-E0020
If you find manual removal too complicated, which is actually complicated and not for everyone, get rid of Windows Foolproof automatically. We suggest using a legitimate antispyware tool which will detect all malicious components of the rogue and will delete them from the system. There are more than 400 files created by the rogue, and all of them have to be deleted. Automatic removal is the best way to get rid of these files and this malware.
In non techie terms:
Windows Foolproof Protector is malicious software which seeks to lure you into paying money and revealing your banking details. Do not hesitate to remove it from the system if you notice it on the computer.
Aliases: WindowsFoolproofProtector.