Do you know what Windows Custom Settings is?
It can be difficult to distinguish between genuine and fake security tools nowadays, but do not fall victim to the Windows Custom Settings rogue antispyware scam. This rogue forms part of the well-known and higly despised Fake Microsoft Security Essentials scam, and emanates from the same family of rogues as Windows Oversight Center and Windows Attention Utility.
This rogue will exploit any possible weakness in order to facilitate its unwarranted entry of the system. This includes using browser hijacking websites to abuse system and browser weaknesses with its drive-by download tactics, as well as bogus online malware scanners. Of late, it has been reported that Windows Custom Settings also uses flash online web ads to distribute its infection.
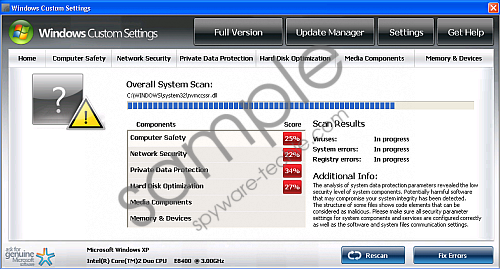
Once Windows Custom Settings roots itself in its host PC, it will edit registry entries so that it loads each time Windows runs. It will then initiate a fake system scan which will inevitably produce false positives of supposed dire infections on the PC – most notably Unknown Win32/Trojan and Backdoor.Win32.Rbot.
As a further attack, Windows Custom Settings will spam the user with incessant fake security alerts in the form of pop ups. These fake alerts will warn the user that his system is being attacked in an effort to get him to pay for Windows Custom Settings’ worthless software, and should be ignored. Other symptoms include poor system performance, increased erratic system behavior and the inability to establish an Internet connection.
In order to take back what is rightfully yours, and minimize the damage this rogue is certain to cause destroy Windows Custom Settings immediately. This can best be achieved by using a genuine security tool which will not only erase Windows Custom Settings but also protect your system against similar future attacks.
In non techie terms:
Windows Custom Settings is a fake security tool which will never live up to any of its promises. Eliminate Windows Custom Settings while there is still time and restore your system’s security.
Aliases: WindowsCustomSettings.